Picture Analysis Tools In CTF | Capture The Flag Series | Reminthink Notes
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]

Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]

Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]

Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]

Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]

Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]
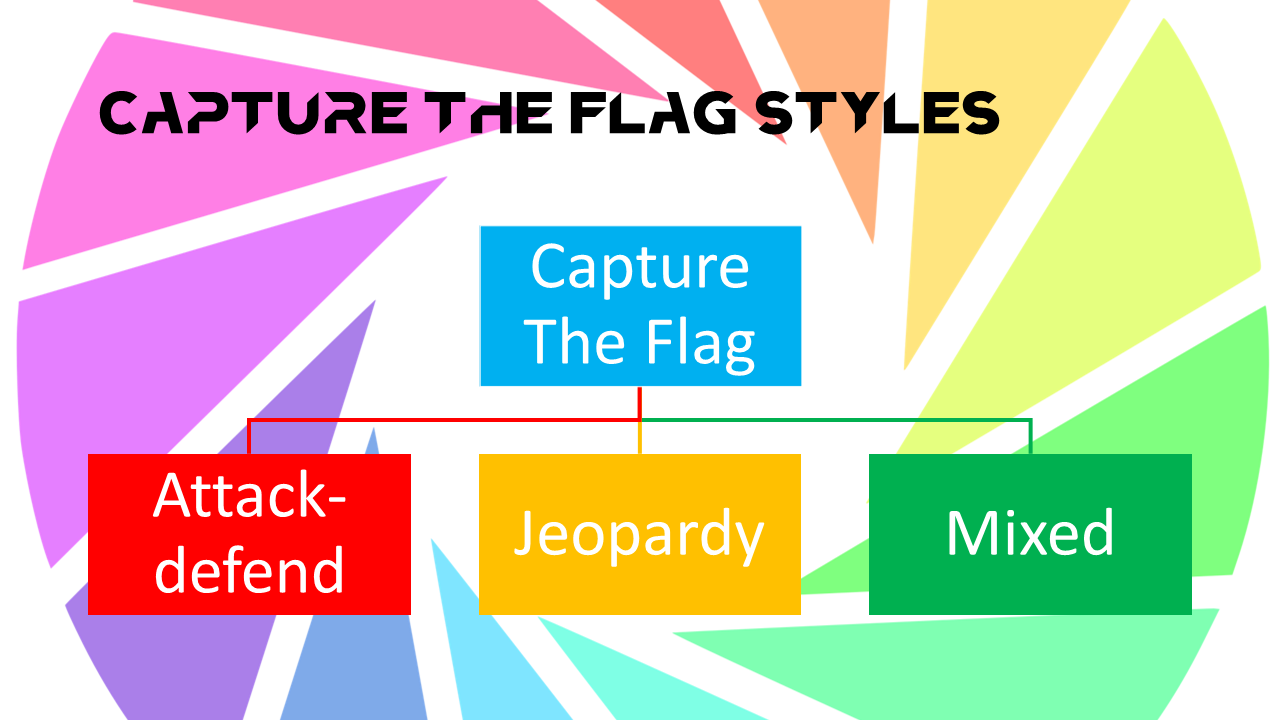
Capture the Flag (CTF) in computer security is an exercise in which “flags” are secretly hidden in purposefully-vulnerable programs or […]